Analytics and Intelligence

‘Darcula’ PhaaS Campaign Sinks Fangs into Victims
A sprawling phishing-as-a-service (PhaaS) campaign that has been running since at least last summer is using more than 20,000 fake domains to target a wide range of organizations in more than 100 ...
Security Boulevard

PyPI Goes Quiet After Huge Malware Attack: 500+ Typosquat Fakes Found
Richi Jennings | | code reuse, open source software supply chain security, PyPI, PyPI malicious packages, pypi vuln, pypi vulnerability, python, Python Malware, Python Packages, Python vulnerability, SB Blogwatch, secure software supply chain, software supply chain, software supply chain attack, software supply chain attacks, software supply chain hygiene, Software supply chain management, software supply chain risk, Software Supply Chain risks, software supply chain security, Software Supply Chain Security Risks, Software Supply Chain Security Weaknesses, typosquat, Typosquatting, typosquatting attacks
Emergency stop button: The Python Package Index was drowning in malicious code again, so they had to shut down registration for cleanup ...
Security Boulevard

Industrial Enterprise Operational Technology Under Threat From Cyberattacks
One in four industrial enterprises had to temporarily cease operations due to cyberattacks within the past year, suggesting operational technology must improve ...
Security Boulevard

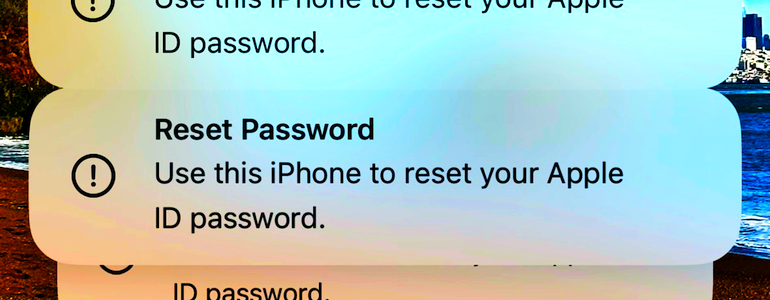
Apple OTP FAIL: ‘MFA Bomb’ Warning — Locks Accounts, Wipes iPhones
Richi Jennings | | 2fa, 2FA bypass, 2FA Flaws, 2FA phishing, 2FA solution, 2FA/MFA, Apple, apple bug, Apple Data Security, apple hack, apple hacker, Apple iCloud, Apple ID, Apple ID failure, Apple iOS, Apple iPad, Apple iPhone, bypass 2FA, MFA, MFA Bombing, mfa fatigue, MFA hacks, mfa protection, mfasecurity, Multi-Factor Authentication (MFA), OTP, OTP circumvention bot, OTP interception bot, phishing-resistant MFA, push otp, SB Blogwatch, TOTP, two-factor-authentication.2fa
Rethink different: First, fatigue frightened users with multiple modal nighttime notifications. Next, call and pretend to be Apple support ...
Security Boulevard

Google: Zero-Day Attacks Rise, Spyware and China are Dangers
The number of zero-day vulnerabilities that are exploited jumped in 2023, with enterprises becoming a larger target and spyware vendors and China-backed cyberespionage groups playing an increasingly bigger role, according to Google ...
Security Boulevard

Checkmarx Aligns With Wiz to Improve Application Security
Checkmarx has integrated its platform for securing application development environments with Wiz's CNAPP ...
Security Boulevard

Hundreds of Clusters Attacked Due to Unpatched Flaw in Ray AI Framework
Thousands of servers running AI workloads are under attack by threat actors exploiting an unpatched vulnerability in the open-source Ray AI framework – widely used by such companies as OpenAI, Uber, Amazon, ...
Security Boulevard

Revealed: Facebook’s “Incredibly Aggressive” Alleged Theft of Snapchat App Data
Richi Jennings | | Brian J. Dunne, class action, class action lawsuit, DeleteFacebook, facebook, facebook fine, free vpn app, Ghostbusters, IAPP, Man In The Middle, man in the middle attack, man in the middle attacks, Mark Zuckerberg, Meta, mitm, MitM Attack, mitm attacks, mitm tool, mitm tools, Onavo, Onavo VPN, SB Blogwatch, Snapchat, SSL Bump, VPN
Meta MITM IAAP SSL bump: Zuck ordered “Project Ghostbusters”—with criminal consequences, says class action lawsuit ...
Security Boulevard

CISA, FBI Push Software Developers to Eliminate SQL Injection Flaws
The federal government is putting pressure on software makers to ensure that their products don’t include SQL injection vulnerabilities, a longtime and ongoing threat that was put in the spotlight with last ...
Security Boulevard

One More Time on SIEM Telemetry / Log Sources …
One More Time on SIEM Telemetry / Log Sources …(cross posted from Dark Reading, and inspired by a previous version of this blog)Cyberpunk IT telemetry via Dall-EFor years, organizations deploying Security Information and Event Management ...